In a series of press releases—no big video event this time—Apple has announced upgrades to the iPad, iPad Pro, and Apple TV. The new models are largely evolutionary, with changes that are welcome but unlikely to change your iPad or Apple TV experience. All are available to order now, with the new iPads arriving on October 26th and the new Apple TV hitting stores on November 4th.
One other note. iPadOS 16 and macOS 13 Ventura ship on October 24th. iPadOS 16 is probably safe to install soon, given the extent to which it’s similar to iOS 16, though the Stage Manager window management feature still has rough edges. Do not upgrade to Ventura until we’ve had a chance to evaluate its stability and compatibility.
New Tenth-Generation iPad Has iPad Air-like Design, Higher Price
The product receiving the most significant changes is the iPad, now in its tenth generation. Apple redesigned it to look and work more like the iPad Air, with squared-off sides, an all-screen design, a 10.9-inch display, USB-C instead of Lightning, and Touch ID in the top button. Also like the iPad Air, the iPad now has a 12-megapixel rear-facing camera and features Wi-Fi 6 plus 5G support in the cellular models for faster connectivity. Perhaps most interestingly, Apple finally repositioned the front-facing 12-megapixel camera along the landscape (long) edge of the iPad so you’ll be looking into the camera for video calls. Oddly, the new iPad Pro models didn’t also receive this improvement.

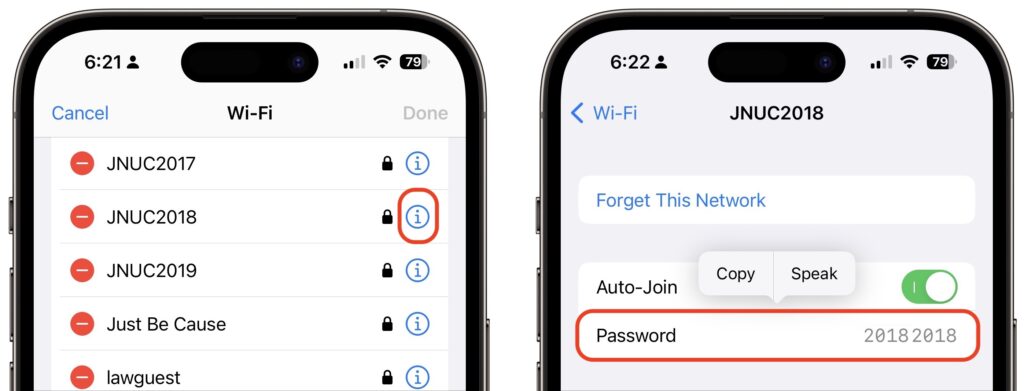
Despite the similarities, the iPad Air retains its technical superiority (and justifies its higher price) in two big ways. First, the tenth-generation iPad relies on the A14 Bionic chip that’s faster than the ninth-generation iPad’s older A13 Bionic but slower than the iPad Air’s higher-performance M1 chip. Second, the tenth-generation iPad remains compatible only with the first-generation Apple Pencil, presumably because Apple left the wireless charging hardware out to cut costs. Since the new iPad switches from Lightning to USB-C, you’ll need a $9 USB-C to Lightning adapter to pair and charge the Lightning-based Apple Pencil—that’s awkward.
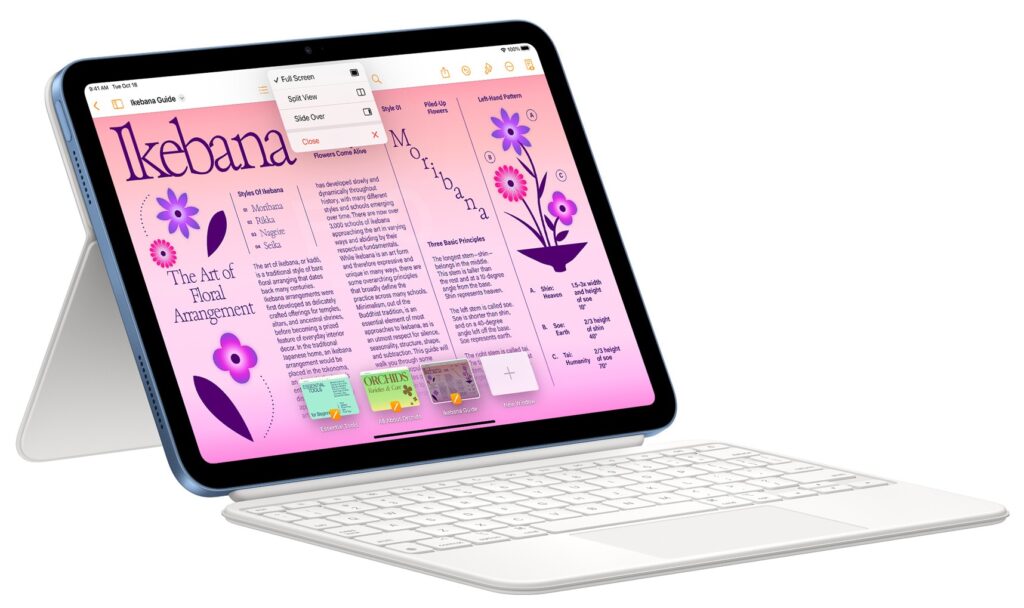
Apple also introduced a new keyboard exclusively for the tenth-generation iPad, the Magic Keyboard Folio. It features full-size keys, a large trackpad, and a 14-key function row. The two-piece design separates the keyboard from the back cover, so you can fold the keyboard behind the iPad or detach it entirely when you’re not using it. The back cover has an adjustable stand for positioning the iPad at several angles. It’s available only in white.

The only problem is that all these changes come at a cost. Historically, the iPad has been Apple’s best value, with the ninth-generation iPad’s price starting at just $329. The new tenth-generation iPad now starts at $449 for the 64 GB Wi-Fi model. Add $150 if you prefer 256 GB of storage, and another $150 if you want cellular capabilities too. You can choose from blue, pink, yellow, and silver finishes.
So now, when pondering a full-size iPad, you have three options. The ninth-generation iPad remains available at $329 for those looking to pay the least. The tenth-generation iPad is now the middle choice at $449. And for those who want a better Apple Pencil experience, faster performance, and slightly better specs, the iPad Air starts at $599.
New iPad Pro Offers M2 Chip, Faster Wi-Fi, and Apple Pencil Hover
Apple has also updated the iPad Pro, but with fewer changes. Foremost among them is Apple’s M2 chip, which provides the iPad Pro with the ultimate in performance. The M2 enables users to capture ProRes video for the first time and to transcode ProRes video up to three times faster than before.
That said, only those already pushing the limits on the previous iPad Pro models should consider upgrading from the previous M1 models since the difference isn’t likely to be that noticeable for less demanding workflows. Similarly rarified is the move to Wi-Fi 6E, which supports wireless networking at up to 2.4 Gbps, or twice as fast as the previous generation. Apple also expanded the 5G networking for the cellular-capable models to support more 5G networks around the world.

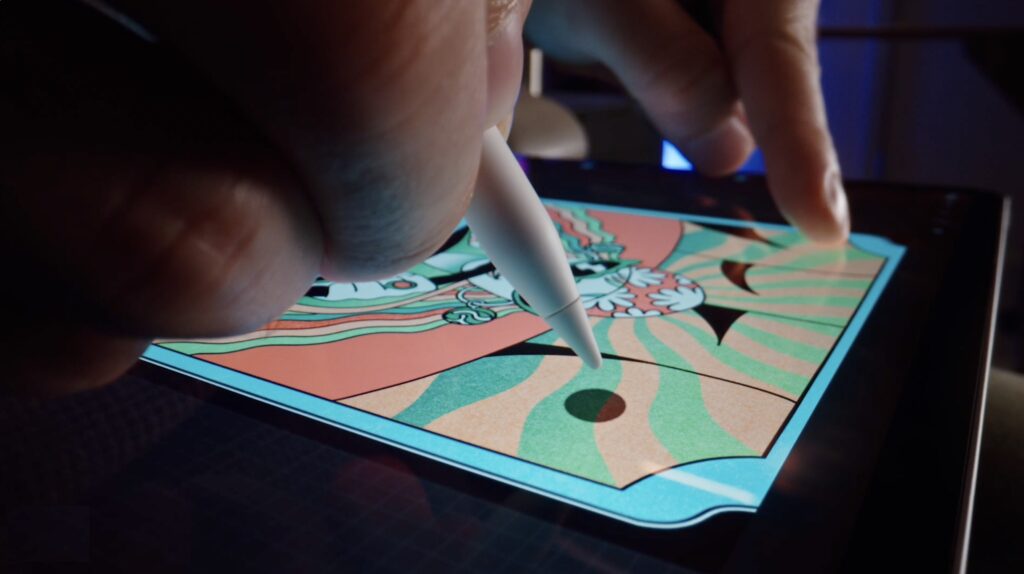
The new iPad Pro can also detect when the second-generation Apple Pencil is hovering up to 12 millimeters above the screen, displaying a circle that helps you position the tip of the Apple Pencil more precisely.

The new iPad Pro retains the same pricing, with the 11-inch model starting at $799 and the 12.9-inch model starting at $1099.
Increasingly, Apple is targeting the iPad Pro at video, audio, and graphics professionals interested in iPad-focused workflows. If that’s you, the new iPad Pro is worthwhile; those just looking for a high-performance iPad would be more economically served by the M1 iPad Air, which is $200 less expensive.
Third-generation Apple TV 4K Boasts Better Specs for Lower Prices
Along with the new iPads, Apple also refreshed its Apple TV lineup, introducing the third-generation Apple TV 4K and dropping the old Apple TV HD. The design remains essentially the same, with the big change being an upgrade from the previous model’s A12 Bionic chip to the faster A15 Bionic for faster performance and more fluid gameplay. Apple also doubled the storage and added support for HDR10+ to provide the best possible video quality across more TVs. Finally, the Siri Remote now charges via USB-C instead of Lightning.

The new Apple TV 4K comes in two models, much like previous generations, but this time there are differences beyond storage, which is important only for apps and games. The $129 Apple TV 4K (Wi-Fi) provides 64 GB of storage and supports only wireless networking, whereas the $149 Apple TV 4K (Wi-Fi + Ethernet) comes with 128 GB of storage, includes a Gigabit Ethernet port for faster wired connectivity, and supports the Thread mesh networking protocol for smart home accessories.
Those prices are $50 lower than the previous generation’s. For those who aren’t interested in Apple TV games, home automation, and wired networking, the $129 Apple TV 4K (Wi-Fi) is significantly more compelling than last year’s more expensive model.
(Featured image by Apple)
Social Media: Apple has released a redesigned tenth-generation iPad with the new Magic Keyboard Folio, new M2 iPad Pro models, and a lower-cost Apple TV 4K with a faster processor and twice the storage. Read on for details: