What Is This “App Tracking Transparency” Apple Added to iOS 14.5?
You’ve likely seen mention of the dispute between Apple and Facebook. It revolves around App Tracking Transparency (ATT), a technology Apple released in iOS 14.5.
The goal of ATT is to give iPhone and iPad users more control over the extent to which app makers can track their data and activities across apps and websites owned by other companies. Before App Tracking Transparency, nothing prevented companies from sucking a vast amount of data about your everyday activities and connecting it to other data to build an insanely detailed picture of who you are and what you do. Apple has written A Day in the Life of Your Data white paper and released the Tracked TV ad to give you a sense of how apps track you. We like to think of app tracking as a fleet of tiny drones constantly hovering over your head, recording your every waking moment for their corporate masters.
Facebook is particularly perturbed by the introduction of App Tracking Transparency because the company makes billions of dollars every year by gleaning as much as it can about you and then selling advertising access to you to companies that want to target people like you. For instance, Facebook knows if you’re a New York City lawyer and divorced mother of two who loves dogs, donates to the Sierra Club, and has Crohn’s disease. Although App Tracking Transparency won’t prevent Facebook from tracking your behavior across its own apps, at least it won’t be able to track you across other companies’ apps and websites.
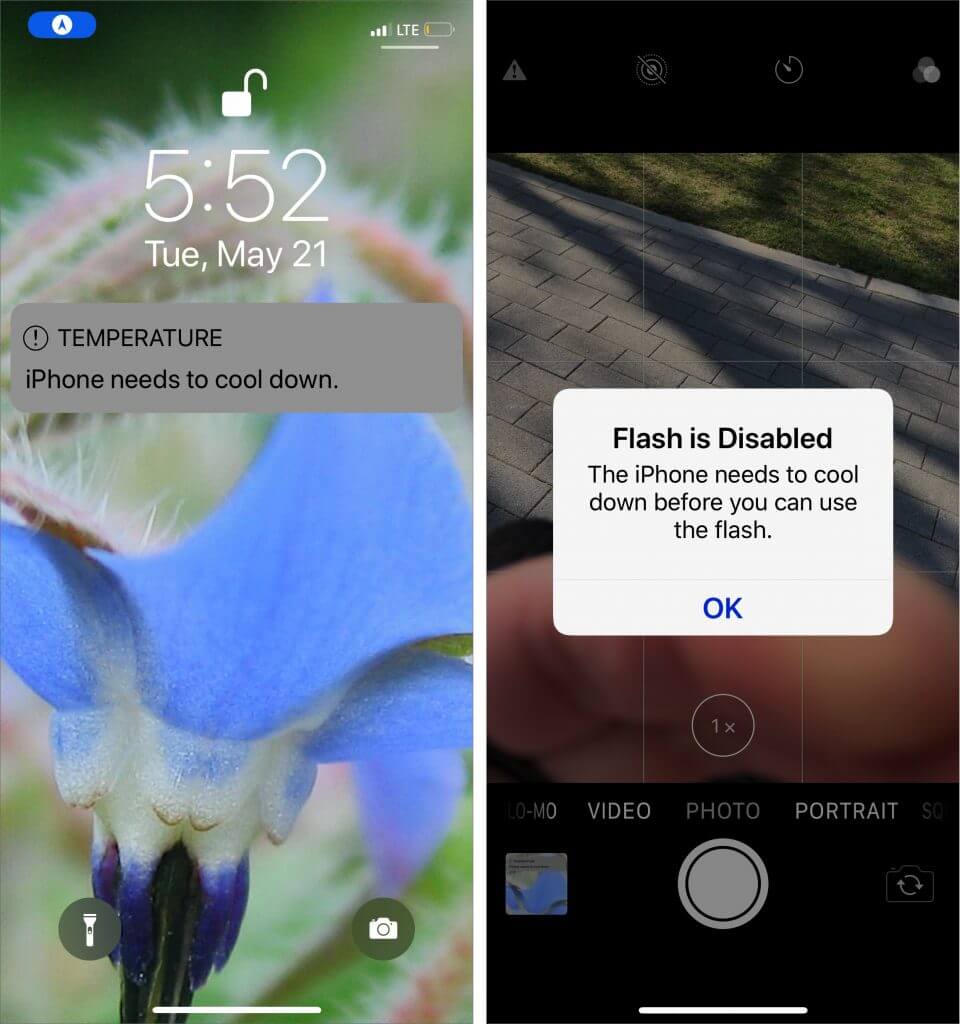
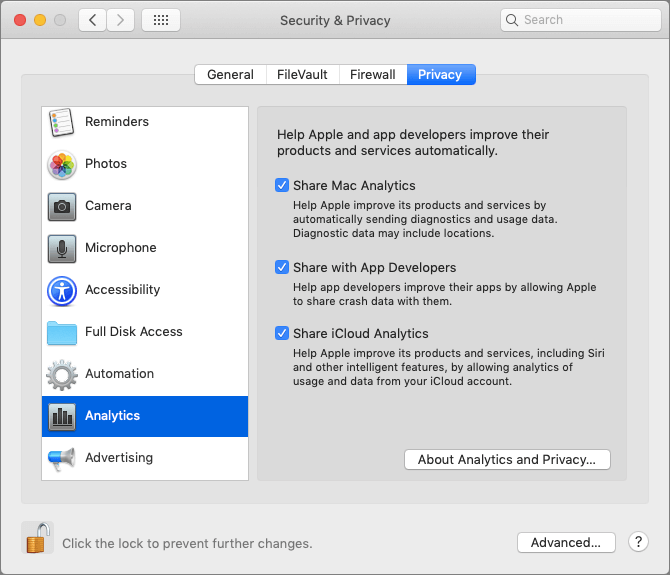
Once you upgrade to the latest version of iOS and iPadOS, App Tracking Transparency requires that apps ask for permission to track you. However, depending on your current privacy settings, you may never see those requests. In Settings > Privacy > Tracking, if Allow Apps to Request to Track is turned off, you won’t receive any permission requests, and apps won’t be able to track you. Turn that setting on, and you’ll start getting alerts that ask for permission.
![]()
Put bluntly, there is absolutely no reason to allow any app to track you. Apple explicitly says that apps may not withhold features from those who opt out of tracking. So if you turn on the Allow Apps to Request to Track setting, tap Ask App Not to Track whenever you’re prompted. If you accidentally tap Allow, you can always go back to Settings > Privacy > Tracking and turn off the switch to rescind permission.
You might want to enable Allow Apps to Request to Track to see which apps were likely violating your privacy before and are still willing to do so even after App Tracking Transparency has exposed their sleazy business practices. Frankly, we’d encourage you to think about whether you want to use apps from such companies—perhaps the best reason to allow the requests is to identify privacy-abusing apps that you’ll then delete.
Early statistics from analytics company Flurry suggest that 94%–96% of users in the United States have opted out of app tracking, either by tapping Ask App Not to Track or by disabling the Allow Apps to Request to Track. We’re surprised the number is so low.
(Featured image by Glen Carrie on Unsplash)
Social Media: New in iOS 14.5 is a privacy-protecting feature called App Tracking Transparency, which forces apps to ask you for permission to track your activities across other apps and websites. Learn more about why you should never allow tracking here: